 This, via the Beeb. Go there for more and video:
This, via the Beeb. Go there for more and video:
USB ‘critically flawed’ after bug discovery, researchers say
Cyber-security experts have dramatically called into question the safety and security of using USB to connect devices to computers.
Berlin-based researchers Karsten Nohl and Jakob Lell demonstrated how any USB device could be used to infect a computer without the user’s knowledge.
The duo said there is no practical way to defend against the vulnerability.
The body responsible for the USB standard said manufacturers could build in extra security.
But Mr Nohl and Mr Lell said the technology was “critically flawed”.
It is not uncommon for USB sticks to be used as a way of getting viruses and other malicious code onto target computers.
You can never trust anything anymore after plugging in a USB stick”
Most famously, the Stuxnet attack on Iranian nuclear centrifuges was believed to have been caused by an infected USB stick.
However, this latest research demonstrated a new level of threat – where a USB device that appears completely empty can still contain malware, even when formatted.
The vulnerability can be used to hide attacks in any kind of USB-connected device – such as a smartphone.
“It may not be the end of the world today,” Mr Nohl told journalists, “but it will affect us, a little bit, every day, for the next 10 years“.
“Basically, you can never trust anything anymore after plugging in a USB stick.” [Of course not all of us are so naïve as to let people plug their gizmos into our computers.]
[…]
The connector is popular due to the fact that it makes it easy to plug in and install a wide variety of devices. Devices that use USB contain a small chip that “tells” the computer exactly what it is, be it a phone, tablet or any other piece of hardware.
It is this function that has been exposed by the threat.
Smartphone ‘hijack’
In one demo, shown off at the Black Hat hackers conference in Las Vegas, a standard USB drive was inserted into a normal computer.Malicious code implanted on the stick tricked the machine into thinking a keyboard had been plugged in.
After just a few moments, the “keyboard” began typing in commands – and instructed the computer to download a malicious program from the internet.
Another demo, shown in detail to the BBC, involved a Samsung smartphone.
When plugged in to charge, the phone would trick the computer into thinking it was in fact a network card. It meant when the user accessed the internet, their browsing was secretly hijacked.
Mr Nohl demonstrated to the BBC how they were able to create a fake copy of PayPal’s website, and steal user log-in details as a result.
Unlike other similar attacks, where simply looking at the web address can give away a scam website, there were no visible clues that a user was under threat.
The same demo could have been carried out on any website, Mr Nohl stressed.
‘Trust nothing’
Mike McLaughlin, a security researcher from First Base Technologies, said the threat should be taken seriously.“USB is ubiquitous across all devices,” he told the BBC.
“It comes down to the same old saying – don’t plug things in that you don’t trust.
“Any business should always have policies in place regarding USB devices and USB drives. Businesses should stop using them if needed.”
[…]
Allow me to dovetail this into what I posted the other day about username and password management. HERE There was a security breach that netted some hackers over a Billion username and passwords combos.
Since I do a lot online, I am careful. Also, within the last 6 months I recall a moment when a friend asked if he could plug his little USB stick into my laptop. I almost came out of my skin. It is not that I don’t trust him, but not everyone is as careful or savvy about what they do with their email and the sites they surf. In another instance, someone gave me a stick with a file on it: I handled that one with tongs too. I look at other people’s USB stick and computers as if they were someone infected with Ebola: handle with extreme care.
This could be a big deal for, say, teachers who accept homework assignments from students on USB drives and, consequently, the students who get them back from the teachers!
There are ways to scan drives for viruses, malware. I don’t think we are yet at the level of checking out the chip in the drive, however. Were I a teacher/student who was constantly swapping USB sticks in and out, I would have a dedicate computer for the task. It would not be connected to my network or the internet. It could be any old computer, not necessarily state of art. I’d look at everything on that computer before I did anything else with it.
Also, on PC, I hold down the SHIFT key when inserting a USB drive. This disables autoplay. Install an antivirus onto the USB drive and scan.
For defending a key from other people tampering with it or getting into it, I have an IronKey which one of you readers sent to me.
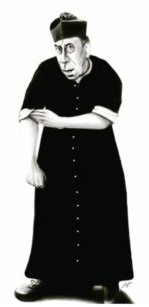
FATHERS! BE CAREFUL! If people have “bad stuff” they could transfer to your computer or your network, or your own USB drive… you are hosed.
I am sure that some of you tech savvy readers could chime in with other ideas and strategies.
Also, given that a lot of life is online these days, I also use the service LifeLock, and I make sure that all my information is updated. I have an affiliate account with LifeLock. You might give it some consideration.
“But Father! But Father!”, some of you are surely hooting. “All this talk of mors improvisa and hackers and EMPs and now USB sticks. You sound paranoid.”
Call it what you want, dear readers. It’s always someone else, until it happens to you.



















Father, as an IT guy for almost 20 years, I will say that I 100% agree with what you have posted here, and I am extremely frightened of this type of attack. Let me further the scenario. Your kid goes to school, uses a USB drive, and then connects their own computer to your home hotspot. One computer can infect other computers on the network as well. This is especially true if you allow sharing across a drive connected to your hotspot (you are using a local backup drive). Access that drive and poof- now you can be infected! Key logger loads on your PC, you type in your username and password for your bank account……poof!
Good antivirus software is a must nowadays. I use Norton 360, and like a lot, because I can scan my Facebook page as well for viruses and malware. McAfee, PCMatic, and if you are cheap, a free one like Avast are also good ones. I also recommend once a weekly scans with Malwarebytes and Superantispyware.
“You sound paranoid.”
Yeah, and what if you are paranoid?
Just because you’re paranoid doesn’t mean it isn’t true.
One thing a tech-savvy person could do is to first test the device with a Linux LiveCD, which is a guest operating system running off of a read-only CD. Boot it on a computer with no internet connection or personal data on it, and then open a terminal. After inserting the USB device, run `dmesg’ and it should tell you what was plugged in, but more importantly, what the device was identified as. If it all checks out you can use it, but if not, then nothing important was put at risk.
Minister Itinerans says: Linux LiveCD
Interesting. I might set up an old laptop with Linux. Haven’t done that yet.
Thanks for this pointer, Father, and especially for your warning to fellow clergy. Our priests (and Religious) don’t need to expose themselves to more nightmare scenarios.
One hopes that chanceries start to become at least as concerned about dangers like this as they have lately been about climbing on board the next politically correct photo op.
For those not familiar with computer technology, here is a brief exposure: all computers run on a basic principle: electricity on vs. electricity off. From that you can develop various possibilities, such as: if the left switch is on, turn on switches no. 3, 5, and 7 – if the right swith is on, turn on 2, 4, and 6. Imagine the exponential number of possibilities such as: if 3, 5 and 7 are on active the following list of 200 switches out of a pool of 25,000.
So everything starts with the simple ON or OFF, which, however, provides no human feedback visible to the eye or audible to the ear, hence there will NEVER be a secure computer. It is like a lock where you press a combination of buttons to open it, but whereas you would get noticed if you were pushing buttons for days on someone’s combination lock – you don’t get noticed if you are checking combinations electronically at a very high speed on someone’s computer.
That is not to say that every computer is being watched by someone, but the possibility of intrusion exists. Here is my advice: for private transactions don’t use the same computer used for casual usage. Instead of disposing of an old Laptop, clean it up and use as your “safe”.
The trouble is that any countermeasure I can think of will have its own set of vulnerabilities associated with it.
The only really secure computer is one with no peripherals (like a monitor, keyboard, mouse), no media, no network connection, and no power. [They are great as planters.]
So best thing you can practically do is mitigate the damage. Yes, hitting shift when you plug a USB drive in your machine is good, but here are a couple of things you can do to minimize the damage.
First, image your system when it is in a known good state. If you go down hard, that is the best way to get up and running quick (obviously provided there is no hardware damage that would need to be repaired quickly).
Second, have a rigorous backup policy at home. So that way you minimize the damage from data loss in between making images.
Now of course, there are a completely different set of risks that clergy must protect against in today’s society. I don’t care to go into them here, but if I was a member of the clergy, i would become very well acquainted with Dropbox (or other similar services) and would only accept files going through such an air gap (i say this because you would only have to deal with the nastiness within a file…nastiness that can be scanned and eliminated fairly easily)
It’s not just flash drives either. My new desktop doesn’t have the old-fashioned serial port or parallel port, so monitor and printer are usb. The laptop that I use at work has a usb wireless mouse. Heck the Android phone charger is usb (either micro or mini, I forget which).
That “billion password” news article is now seeming to be fake – a marketing ploy by an unknown security company. However, the idea is plausible.
As for USB – Markomalley’s advice us right on – the average person should do what’s reasonable for their knowledge level – not share usb sticks, current software and virus protection, not write down passwords.
Those of us in Information Security know that there are so many vectors (a usb coffee warmer can be hacked) – that for secure computer at work, we epoxy the USB ports closed, and even so, there’s no guarantee. For our personal stuff we keep an eye on things and realize that people are watching us. I like the idea of lifelock to protect against thieves, but there are worse evils than just theft. There are webites I *will not* visit, even though they are not immoral or illegal, because I’m assuming someone’s looking over my shoulder and it will be intentionally misinterpreted.
This is where a good anti-virus program can come in. Most, if not all, allow you set set specific policies (such as disallowing remote code execution via external devices (i.e. flash drives)). Otherwise, the same thing can be done via local Windoze policies via the MMC console.
If I am not mistaken, the infamous Stuxnet Trojan Horse that infected the Siemens workstations in Iran was launched via a thumb drive. These workstations controlled the manufacturing of the centrifuges used by the Iranian nuclear weapons program.
I note that Norton and McAfee are mentioned here.
I run (paid yearly) AVG…..does anyone know how good it is or anything about it.Seems to work well for me but am no computer expert.
Merci
But Father! But Father! Can I not just go around sticking whatever I want in whatever I want? You just hate sharing, that’s all!
More seriously, I note that two USB sticks still cannot exchange data by themselves…
OK, actually seriously, do take the Linux suggestion above. Don’t get lost in the world of competing distros, just pick one and learn a bit about it.
I guess it is time for me to shut this computer thing down… go out the barn, saddle up my horse and ride into town so my mail can catch the next pony express. In the mean time I’ll send a message via that new fangled morse code to the family on the other side of the state.
Oh well, time to blow out the candles and go to bed. Good to not have that ‘tek no lo gee’
It’s bad, but it’s not indefensible.
One possible defense (I think it would have to be implemented on an OS level) would be a security prompt when plugging in a USB device.
Basically something which would say “You just plugged in a USB device, which claims to be (1) a storage device, (2) a keyboard, (3) a network card.”
This would have to happen before any of the drivers were permitted to run. Then you could individually allow and/or block any of those functions.
I just scan my memory sticks with Norton.
My paypal account got hacked several years back and whomever did it, tried to make a $700 purchase on my credit card. Since then, I don’t conduct business over the internet. I use it to window shop and then look for an 800# on the shopping site so that I can phone in my order. I also never bank online. However, this makes it tough to send donations to a wonderful priest who does everything online! Father, do you have a P.O. Box or something set up for the tech-allergic who wish to send you items and donations?
My experience: I used Norton AV for years until I was infected. I then switched to McAfee for years until I got infected. (Both apps automatically updated virus defs several times per day.) I then switched to the free version of AVAST AV. I’ve been using it for a few years now with no issues. And it has blocked several malware infection attempts automatically! I like it. It also works on Android devices. And it scans USB and external drives.
While I don’t doubt what the researchers have said, I think that if I were trying to spread malware, the previously existing methods are working quite well and are far more of a threat. The typical computer user may never connect a phone or flash drive to his computer, but he is always clicking on web sites and opening e-mails, and with Internet the way it is, with most web sites not working properly unless you let them reprogram your computer– malware authors probably wouldn’t have to waste time with USB drives. In another year or two USB will probably be replaced by KJF or WQL or something else anyway.
Word to the wisely paranoid, friends: I recommend going as far as not indicating on public forums which particular Antivirus package I use. They occasionally have weaknesses which are exploitable, and social-engineering is the easiest method of all: you save the hacker a lot of work if you tell him up-front how you’re secured.
If you let others (like kids) use your internet-connection (via a wireless hub, say) learn how to configure the DMZ, and place them on there. Disable ‘autorun’ on all external drives, and always scan a new file before running it.
If you must let your kids or friends use your computer then create separate standard accounts for them, which then require the administrator password to be entered before installing software. Three good things come from this, first nothing gets installed without your knowledge; second, you know what they’re playing at when they start whining that their favourite games site doesn’t work; third, anything they do install is limited to that user account only, and runs only with their (limited) privileges, while deleting the account deletes all the settings associated with it. Even then, it’s far from perfect.
Trust nothing, and if in doubt don’t run it.
There is definitely a risk here, but I think it’s being somewhat exaggerated.
1) The BBC video shows a USB exploit to make man-in-the-middle attacks on connections to websites. Since HTTPS prevents man-in-the-middle attacks, the attack only works for websites to which you connect via HTTP. You should not connect to any sensitive or financial website (like PayPal) via HTTP, yet this is what has been done in the video (look carefully at the browser address bar). Using the HTTP Everywhere browser extension is one way to make this sort of attack more difficult.
2) A USB stick can only be used for this exploit if it allows its firmware to be replaced with firmware not produced by the manufacturer. If the stick does not support firmware updates, or only accepts firmware updates that are cryptographically signed, it is safe from the problem reported. It would be interesting to know what percentage of devices fall into the latter category, but some certainly do (IronKey’s maker is advertising its immunity). If you only use USB sticks known to be immune, then you don’t have to worry about this problem (unless you’re targeted by someone clever enough to crack open the memory stick casing and put a different chip inside).